So what is VPN really? The generally utilized “VPN” stands for the term Virtual Private Network. In its most essential definition a VPN is a system of PCs which is kept private and secure in spite of being spread crosswise over unsecured open systems, for example, the web.
VPN alludes to an arrangement of innovations that empower a PC to interface with a private system by means of Internet (or other open system) and trade information with different PCs on that system safely as though it was physically a portion of it. This is generally accomplished by setting up a scrambled association with a remote PC and “burrowing” all the movement by means of that association. While VPNs are utilized for a wide range of purposes, “VPN administration” most generally alludes to a supplier of VPN network that is utilized to burrow all Internet movement past the nearby ISP.
What is VPN (Virtual Private Network)?
A Virtual Private Network (VPN) is a private PC system built inside of an open system, (for example, the worldwide Internet). Envision a VPN as a passage interfacing you to the Internet through your VPN administration; on one side is your PC, and on the other side is your VPN provider’s server. On the off chance that somebody takes a gander at the passage from the outside they see just the passage, and the movement inside stays covered up. When you utilize a VPN, sites you visit see just your VPN providers IP (Internet Protocol) address, so your genuine IP address and your action stay avoided whatever is left of the world. Anybody sniffing your movement (your ISP, law implementation, or pernicious programmers, for instance) will see just scrambled information.
In any case, your VPN supplier, by configuration, has admittance to your Internet action and can log data, for example, the IP address you are interfacing from, association begin and end times, or whatever other data they are occupied with.
Keeping messages private is a worldwide demand these days:
The fundamental reason for a VPN is to do only that, to keep your information private. On the off chance that you shop online or join with your bank by means of the Internet, at whatever points you see https rather than http, you are now utilizing a VPN, yet a coordinated VPN. From your PC to the https-server, the information traded between the two is encoded.
Understand that the yearning for security has nothing to do with taking part in unlawful movement. Security is superbly legitimate. The contention that you don’t need to stress over your security in the event that you don’t have anything to cover up is unreasonable, and frequently utilized by government and law implementation to facilitate their motivation, effectively blurring the main problems.
So, can anybody use VPN?
Everybody who handles secret data, or who has a need to keep their exercises and data private uses VPNs. This incorporates not just law authorization, fire divisions, numerous other government elements, banks and different partnerships, additionally legal counsellors, specialists and numerous business explorers.
VPNs have as of late gotten to be prevalent in the customer space. Initially utilized by document sharers to conceal their characters when pilfering copyright ensured content, purchasers now utilize VPNs to secure their protection when associating with open Wi-Fi, at any café or to access destinations and administrations numerous legislatures square to subdue disagree and confine the free stream of data. VPNs additionally empower access to locale confined substance, for example, Netflix, Hulu, or Pandora.
A great many people utilize a VPN for one of three reasons, or a mix of all
1. To secure their web movement from prying eyes. For instance, joining with interpersonal organizations or sending email from your neighborhood coffeehouse without worry that the dreadful gentleman by you is covertly getting to your passwords or private interchanges.
2. Obscurity on the Internet. For instance, to skim the web without uncovering your character or being followed, i.e., seeing sites containing data uncomfortable for your legislature without apprehension of your front entryway being thumped down in light of it.
3. Accessing area confined substance. Most VPN administrations make it conceivable to view area confined substance safely, yet not every one of them ensure your security totally.
What do PPTP, L2TP and OpenVPN mean? What is VPN protocol?
How much protection you need decides the level of security you require. You can keep your own data 100% private on the off chance that you don’t unite with any system you don’t 100% control. At the point when that is not down to earth you need to utilize arrangements like VPNs to secure your protection.
The three most basic Point-to-Point Protocols used to associate with a VPN are: Point-to-Point Tunnelling Protocol (PPTP), Layer 2 Tunnelling Protocol (L2TP) and OpenVPN.
Further reading: https://www.waselpro.com/en/faq/44/
a. PPTP, initially created by a consortium including Microsoft is the most generally disseminated convention.
b. L2TP is a half breed of Layer 2 Forwarding (L2F) and the best of PPTP.
c. OpenVPN is an open source convention created by OpenVPN Technologies, Inc.
Confused yet? Don’t be, all you truly need to know is that PPTP has been hacked, L2TP is most secure when utilized with IPSec, and OpenVPN offers the largest amount of security. Every convention has its own particular advantages and disadvantages, and what convention you ought to utilize relies on upon what gadgets you need to utilize it on, and what administrations your VPN supplier offers.
What is SSH Protocol? How-To Choose a VPN Provider?
Looking at the quantity of administrations accessible will make your head turn. So how are you expected to pick the best supplier?
Begin with considering your needs:
a. If you’re fundamental objective is to watch area confined amusement online pretty much any VPN supplier will do, and speed will be your principle concern.
b. If your fundamental concern is the security of your association while getting to open Wi-Fi, or you just don’t need your ISP to comprehend what you are doing, once more, any supplier will do.
c. If namelessness is your primary need pick a non-logging VPN supplier that offers encryption.
d. If you live in a nation with prohibitive Internet get to, the inquiry will be which VPN suppliers you would be able to reach. Pick a non-logging VPN supplier offering encryption and mysterious instalment routines to ensure your personality does not fall into the wrong hands.
Then you ought to consider:
Whether the administration incorporates VPN end focuses in one or more nations
What conventions are given?(L2TP, OpenVPN, SSH… etc.)
The level of security.
The span of the IP location pool utilized for VPN associations
Whether your association subtle elements are logged or erased quickly after you end a VPN
Whether the VPN framework incorporates hostile to malware and against spyware assurance
Support for cell phones
Dependability and transfer speed
Cost
NOTE: There are various “free” VPN administration suppliers that give constrained administrations and increase income by serving you with ads while you’re associated with the VPN.
No matter which VPN supplier you pick, it is constantly useful to consider the following:
How much do you believe a VPN provider’s guarantees of either not logging, or cleansing their logs as often as sufficiently possible to ensure your namelessness? Proclamations like we don’t keep any logs trailed by we will suspend any users account in the event that we decide they take part in illicit activity unquestionably make me wonder
We urge you to painstakingly read each VPN providers Terms & Conditions explanation and Privacy Policy as they are not as clear as they may show up, and can be deluding. Likewise, check evaluating and hunt down rebates and coupons. Regularly you will discover huge rebates or different arrangements to bring down the cost.
Check out which nations your forthcoming supplier has servers in, which working frameworks they bolster, whether they permit simultaneous associations, and whether you can utilize your record with various devices.
If obscurity is your fundamental concern look at which instalment strategies the VPN supplier acknowledges. Paying with a charge card in your name clearly destroys your obscurity right. Luckily, more suppliers acknowledge PayPal, Payza or other more unknown instalment options.
Next, sign up for a free trial account. Most VPN suppliers will permit you to do that without requiring a MasterCard or individual data. Along these lines you can test the VPN from your PC and with those sites and administrations you consistently utilize, making it simple to choose if a supplier will address your issues or not.
Finally, if a supplier meets all your criteria and functioned admirably amid your trial, consider agreeing to a paid account.
Conclusion
Picking the privilege VPN supplier from a dumbfounding exhibit of decisions can appear to be overwhelming, yet once you make sense of what you truly require it is generally simple:
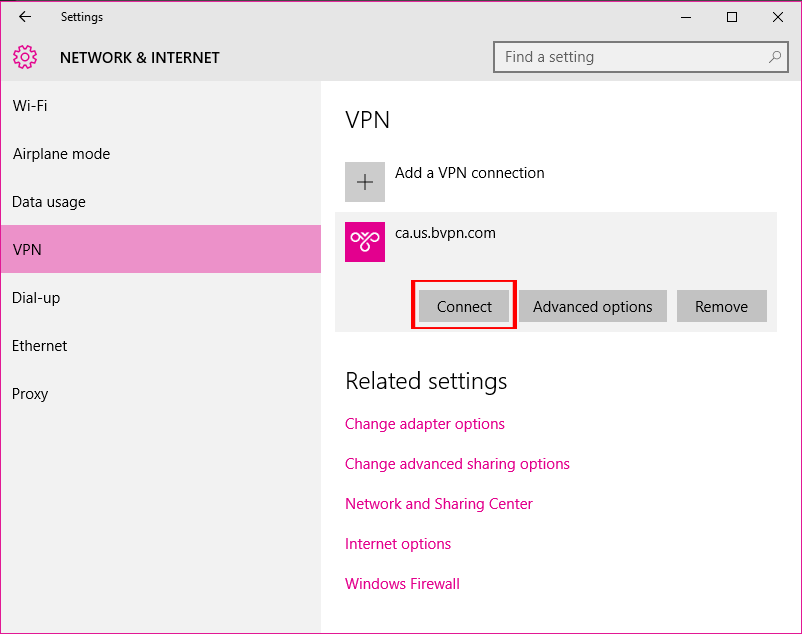
If namelessness is your essential concern you ought to dependably pick a Non-Logging VPN. I utilize BVPN, a supplier that claims not to log anything.
If you require just securing your Wi-Fi association or detour local confinements to watch recordings, I would prescribe iWasel it has servers in such a variety of nations that regardless of where you are or where you need to associate with, they have you covered.